Secure encoding requires secure keys. Instead of generating these keys with special methods via the internet, for instance, KIT re-searchers propose to automatically generate them during personal encounters and to pass them on from smartphone to smartphone. The keys are remodified at every encounter, such that a message can only be read by both conversation partners. “When using these keys exchanged via personal encounters, tapping is much more difficult. An attacker must have corrupted one of the devices in the chain in order to know the key. When combining this method with today’s technologies, the expenditure required for mass surveillance is increased considerably,” Professor Jörn Müller-Quade, Head of the KIT Cryptography and Security Working Group, explains.
Key Exchange in Social Networks
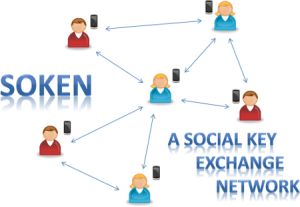
Key exchange follows the social network of its users: Only those who encounter in reality do exchange the keys. In this way, keys are passed on from friends to friends of friends, and so on. Thanks to these friendships, even not so close friends can communicate in a securely encoded manner. The more common friends two users have, the higher is the probablility of smartphones infected by specialized viruses or trojans being no longer able to calculate the key used for communication in a chain.
“Our simulations have shown that even in case of many infected smartphones, large parts of the communication processes are pro-tected reliably against tapping,” Dirk Achenbach, another member of the group, adds.
This is due to the fact that the system generates a new key whenever a new encounter of two persons takes place. If only one of these keys reaches the recipient via a path without an infected smartphone, subsequent communication is secure. In the own social network, keys may be exchanged constantly with long-term security. A group of students has already developed a prototype in the seminar “Praxis der Software-Entwicklung” (Practice of Software Development) offered by the Department of Informatics. Professor Müller-Quade, however, cannot estimate when such a system will be available on the market.
Tips for IT Security: Anti-Prism Party on February 12, 2014
According to Müller-Quade, anybody should think about how own communication channels can be protected against attacks and data theft. “At the moment, there is no 100% safety. But with a few means, everyone of us can contribute to making the work of data thieves much more difficult.” To present these often simple and cost-free means, the working group, together with the Karlsruhe IT Security Initiative (KA-IT-SI) and the Center for Art and Media (ZKM), Karlsruhe, will organize an encoding party on February 12, 2014. During the party, various options for digital self-protection will be presented and explained.
Information on the party: http://www.anti-prism-party.de/